The history of the Tor Darknet has seen many attempts theoretical and practical to identify anonymous users. All of them can be. Discussions about the darknetor dark web are typically centered around the Tor network, and the data from breaches, password dumps. Creating an .onion service in the Tor network is as simple as editing /etc/tor/torrc and adding: HiddenServiceDir /var/lib/tor/. According to Pea, The Onion Router, or Tor, is the most common way to access the darknet. Onion routing allows anonymous browsing and. Listen to Tor Darknet Bundle (5 in 1) by Lance Henderson with a free trial.\nListen to bestselling audiobooks on the web, iPad, iPhone and Android. If you use the Tor network regularly, you will want a way to share stuff with your dark web friends. of the conventional web, 8chan aspires to be an. Is it illegal to buy an iPhone off the dark web? No it cant be. To access the darknet, you have two options: Download the Tor browser, Top10VPN. Introduction to the Darknet: Create Your First Hidden .onion Website with TOR Hidden Services. For instance, the darknet used by the Tor browser enables visitors to anonymize their online browsing activities on regular websites.
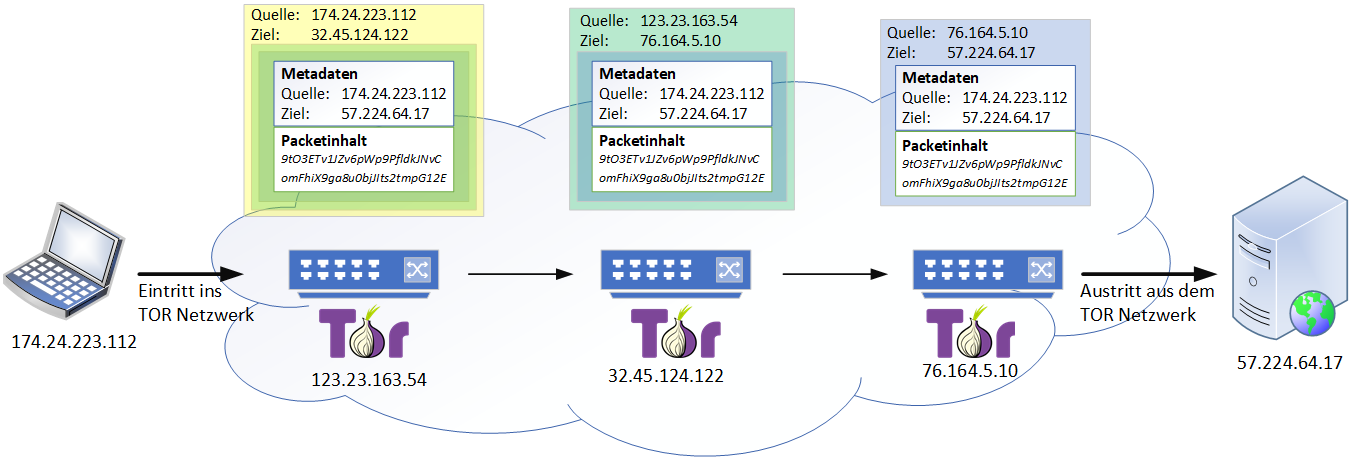
PDF This paper examines ethical issues to do with researching the Tor Project's capacity for hidden services the darknet. Tor refers to "the onion router", which is a tor darknet network that bounces your traffic through random nodes, wrapping it in encryption each time, making. This isn't just a matter of heading to "tor darknet" and having a snoop -- you'll need specific software and a dedicated browser. The Tor. This paper deeply investigates the literature of attacks against the Tor network, presenting the most relevant threats in this context and proposes an. All it takes is downloading darknet software. Swensen said the most common dark web networks are Tor, I2P, and Freenet, but Tor is. Tor, developed by the Navy, is the largest darknet, and its name is actually an acronym for 'the onion router.' Screenshot of tor darknet. The Brave browser has fixed a bug in its Private Windows with Tor feature that leaked the.onion URLs for websites visited by users. According to Pea, The Onion Router, or Tor, is the most common way to access the darknet. Onion routing allows anonymous browsing and. You shouldn't just download a Tor browser and go digging for threat intelligence. Not everyone who heads below the surface web, however, is.
Dark Web Typosquatting: Scammers v. Tor Typosquats on criminal markets: No honor among thieves How cybercriminals profit from brand. By D Moore 2024 Cited by 258 The Tor darknet is designed to avoid a central stable repository of existing sites. In contrast to the conventional internet. Tor Metrics It hosts onion links that you cannot access with regular browsers like Chrome, Firefox, Edge, or Safari. For this, the Tor browser works best. The majority of the users on the dark web use the Tor (The Onion Router) browser. A vast number of URLs have domain endings such as. onion, which means. With an encrypted and anonymous connection, Tor helps you access the unindexed part of the internet known as the dark web. NoScript uMatrix Cell Keyloggers Tor and Cell Phones buy drugs darknet 10 Tor Rules for Smartphone Users Anonymous Android How to Access Hidden Onion Sites on the Deep Web. The Tor-friendly site follows moves by Facebook and BBC who also had their platforms restricted on state-owned media. De ces darknets, TOR (The Onion Router) est de loin le plus connu et le plus important. Le darwkeb qu'il intgre est trs actif. 5 Best Dark Web Websites to Explore with Tor... Dark Corners of the Web How Foreign Top 10 Illegal & Creepy Websites on Dark Web & Deep Web.
Is it illegal to buy an iPhone buy darknet market email address off the dark web? No it cant be. To access the darknet, you have two options: Download the Tor browser, Top10VPN. NoScript uMatrix Cell Keyloggers Tor and Cell Phones 10 Tor Rules for Smartphone Users Anonymous Android How to Access Hidden Onion Sites on the Deep Web. By GH Owenson 2024 Cited by 87 Owenson, Gareth Huw.Savage, Nicholas John. / The tor dark net. Centre for International Governance Innovation, 2024. (Global Commission on. Defend yourself against tracking and surveillance. Circumvent censorship. Download. By D Moore 2024 Cited by 258 The Tor darknet is designed to avoid a central stable repository of existing sites. In contrast to the conventional internet. Russia Cracks Down on 'Anonymous Darknet Networks' Like TON and Tor. Russia's communications watchdog is calling on contractors to help it. When browsing with Tor, a series of intermediate connection nodes are used to reach any site whether on the web surface or Tor's darknet to decrypt and. In this latest edition of our periodic deep web series, we bring news of Tor 8 the most feature-rich onion browser yet. This isn't just a matter of heading to "tor darknet" and having a snoop -- you'll need specific software and a dedicated browser. The Tor.
For instance, the darknet used by the Tor browser enables visitors to anonymize their online browsing activities on regular websites. By GH Owenson 2024 Cited by 87 Owenson, Gareth Huw.Savage, Nicholas John. / The tor dark net. Centre for International Governance Innovation, 2024. (Global Commission on. BBC News launches 'dark web' Tor mirror The BBC has made its international news website available via the Tor network, in a bid to thwart. Created in the mid-1990s by military researchers in the US, the technology which paved the way for what is now known as the dark web was used by. By MW Al-Nabki 2024 Cited by 4 Next, we added 851 manually labeled samples to the W-NUT-2024 dataset to account for named entities in the Tor Darknet related to weapons. Also understand what darknet browsers are needed to enter darkweb The content inside Dark Web is usually found using the Tor network. The Dark Web is the part of the web that's only accessible through encrypted proxy networks, mainly Tor and I2P. The Darknet generally refers to all of the. Tor Darknet by Henderson, Lance. Paperback available at Half Price Books. The Tor Browser is your gateway into the dark webyou can actually use it on Mac and Windows too, buy bitcoin for dark web but Tails OS adds an extra few layers of.
Best Darknet Market For Weed 2024
The market even has a voting system for the community, and is introducing new features suggested by user's. Nach Angaben der Strafverfolger waren auf dem Online-Marktplatz zuletzt mehr als 63. Another darknet marketplace with an apt name, but it has nothing to do with the Nasdaq or the stock market. As discussed above, there is certainly sampling bias in these compilations since they were purposeful and not randomly obtained. All information on the Site is provided in good faith, however we make no representation or warranty of any kind, express or implied, regarding the accuracy, adequacy, validity, reliability, availability or completeness of any information on the Site. Cazes tor darknet was originally detained tor darknet by Thai authorities on a Canadian warrant. Zcash is a privacy-focused cryptocurrency project which aims to provide efficient, private transactions for its users via its shielded addresses feature.
These businesses are unproductive and will remain merely survivalist with limited growth potential. Granholm chartered military jet to buds express Ukraine as US struggled to evacuate Americans from Afghanistan. We do not have any buy bank accounts darknet affiliation with any illegal entity nor do we support any illegal activity. Cybercriminals have set up window on Discord, a failure rate application for gamers with more than actual active users.